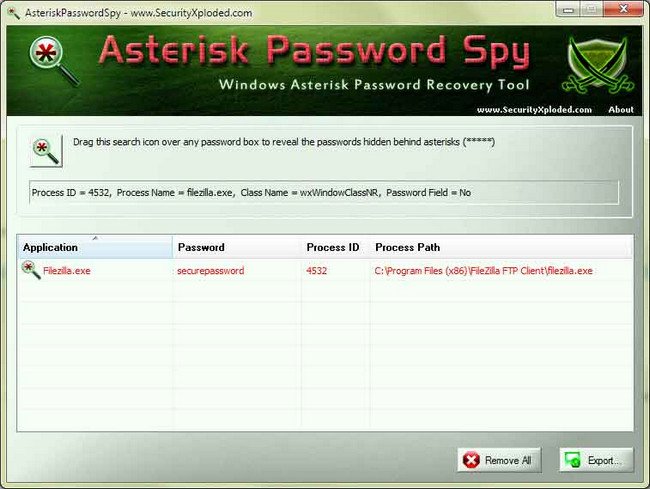
Download Asterisk Password Spy 12 full version program free setup for Windows. Asterisk Password Spy is the free tool to instantly reveal the hidden password behind asterisks (*****).
Asterisk Password Spy Overview
Asterisk Password Spy is a term often used to refer to a type of software or tool that is designed to reveal or recover passwords that are obscured by asterisks or dots in password fields. These password fields are commonly found in various applications, including web browsers, email clients, and login screens. While the term itself may sound intriguing, it’s important to note that the use of such tools can raise ethical and privacy concerns. Asterisk Password Spy tools are primarily used for the legitimate purpose of recovering forgotten or obscured passwords. When you enter a password in a login field, it is often obscured with asterisks or dots for security reasons. These tools can reveal the actual characters behind the masking. In certain situations, such as when you’ve forgotten a password for a site or application, these tools can be helpful for password recovery. They can save users from the frustration of resetting passwords or contacting support. While Asterisk Password Spy tools have valid use cases, they also raise significant security and privacy concerns. If misused, they can be employed to capture someone else’s passwords without their consent, potentially leading to unauthorized access and privacy violations. It’s crucial to use such tools ethically and responsibly. Attempting to reveal someone else’s password without their permission is unethical and may be illegal, depending on your jurisdiction. You may also like XToolBox 2.9
It’s important to respect legal and ethical boundaries when using Asterisk Password Spy tools. Always ensure you have the rightful authority to access and recover passwords. In most cases, it is advisable to use official password recovery methods provided by websites or applications rather than resorting to password-revealing tools. These methods typically include password reset options through email or security questions. A more secure and practical approach to dealing with forgotten passwords is to use a reputable password manager. These tools securely store and manage passwords, making it easier to generate strong, unique passwords and recover them when necessary. In summary, Asterisk Password Spy tools have a valid purpose in password recovery, but their use should be approached with caution and a strong sense of ethics. It’s crucial to ensure that you are using such tools only for legitimate and authorized purposes and that you are not infringing upon anyone’s privacy or security. Always prioritize security and respect for others’ privacy when dealing with password-related issues.
Features
- 1. Password Recovery: Asterisk Password Spy tools are primarily designed to recover obscured passwords entered in password fields.
- 2. Compatibility: These tools can work with various applications, including web browsers, email clients, and login screens.
- 3. User-Friendly Interface: Most Asterisk Password Spy tools offer a user-friendly interface for easy operation.
- 4. Password Unmasking: They reveal the actual characters behind the asterisks or dots in password fields.
- 5. Real-Time Detection: Many tools can detect and reveal passwords in real-time as you type.
- 6. Multi-Language Support: Some tools support multiple languages, catering to a global user base.
- 7. Customization: Users may have options to customize the tool’s behavior and appearance.
- 8. Password Field Detection: The tool can automatically identify password fields on websites and applications.
- 9. Clipboard Support: Some tools allow users to copy revealed passwords to the clipboard for easy pasting.
- 10. Offline Use: Most Asterisk Password Spy tools operate offline, ensuring privacy and security.
- 11. Lightweight: They are typically lightweight and don’t consume significant system resources.
- 12. Compatibility with Windows: Many tools are designed to work seamlessly with Windows operating systems.
- 13. Portable Versions: Some tools offer portable versions that can be run from a USB drive.
- 14. Security Considerations: These tools should be used responsibly and ethically, respecting privacy and legal boundaries.
- 15. No Hidden Costs: Genuine Asterisk Password Spy tools are usually free and don’t impose hidden charges.
- 16. Respect Copyright: Users should only use these tools for password recovery on accounts for which they have legitimate access rights.
- 17. Legal Use: They are intended for legal and authorized purposes, such as recovering forgotten passwords.
- 18. Safety Measures: Reputable tools ensure that revealed passwords are not stored or logged.
- 19. Encrypted Connections: Some tools use secure and encrypted connections to protect user data.
- 20. Online Tutorials: Some tools offer online tutorials or guides for assistance.
- 21. Regular Updates: Updates may be provided to improve performance and security.
- 22. No Registration: Most tools don’t require users to register or provide personal information.
- 23. Technical Support: Some tools offer customer support to address user queries or issues.
- 24. Browser Compatibility: They work with various web browsers, such as Chrome, Firefox, and Edge.
- 25. Email Client Support: Can reveal email client passwords for email retrieval.
- 26. Password Field Indicators: Some tools visually indicate password fields, making them easy to identify.
- 27. Multi-Platform Support: A few tools are cross-platform and work on Windows, macOS, and Linux.
- 28. Password Backup: Users can back up revealed passwords securely.
- 29. Uninstallation: Easy removal of the software when no longer needed.
- 30. Automatic Updates: Some tools can automatically check for and apply updates.
- 31. Export Passwords: Users can export revealed passwords to secure storage.
- 32. Secure Password Storage: Reputable tools ensure that revealed passwords are stored securely.
- 33. Technical Documentation: Access to user guides or manuals for assistance.
- 34. Network Passwords: Some tools can reveal network passwords for Wi-Fi access.
- 35. Encrypted PDFs: They may work with password-protected and encrypted PDF files.
- 36. Command-Line Support: Some tools offer command-line functionality for advanced users.
- 37. Multifunctional: Can reveal passwords for various types of accounts, including social media, email, and banking.
- 38. Clear Text Display: Some tools may provide an option to display revealed passwords in clear text.
- 39. Safe Usage Guidelines: Reputable tools often include guidelines on safe and ethical usage.
Technical Details
- Software Name: Asterisk Password Spy for Windows
- Software File Name: Asterisk-Password-Spy-12.0.rar
- Software Version: 12.0
- File Size: 3.24 MB
- Developers: securityxploded
- File Password: 123
- Language: Multilingual
- Working Mode: Offline (You donÆt need an internet connection to use it after installing)
System Requirements
- Operating System: Win 7, 8, 10, 11
- Free Hard Disk Space:
- Installed Memory: 1 GB
- Processor: Intel Dual Core processor or later
- Minimum Screen Resolution: 800 x 600
What is the latest version of Asterisk Password Spy?
The developers consistently update the project. You can view the most recent software update on their official website.
Is it worth it to install and use Software Asterisk Password Spy?
Whether an app is worth using or not depends on several factors, such as its functionality, features, ease of use, reliability, and value for money.
To determine if an app is worth using, you should consider the following:
- Functionality and features: Does the app provide the features and functionality you need? Does it offer any additional features that you would find useful?
- Ease of use: Is the app user-friendly and easy to navigate? Can you easily find the features you need without getting lost in the interface?
- Reliability and performance: Does the app work reliably and consistently? Does it crash or freeze frequently? Does it run smoothly and efficiently?
- Reviews and ratings: Check out reviews and ratings from other users to see what their experiences have been like with the app.
Based on these factors, you can decide if an app is worth using or not. If the app meets your needs, is user-friendly, works reliably, and offers good value for money and time, then it may be worth using.
Is Asterisk Password Spy Safe?
Asterisk Password Spy is widely used on Windows operating systems. In terms of safety, it is generally considered to be a safe and reliable software program. However, it’s important to download it from a reputable source, such as the official website or a trusted download site, to ensure that you are getting a genuine version of the software. There have been instances where attackers have used fake or modified versions of software to distribute malware, so it’s essential to be vigilant and cautious when downloading and installing the software. Overall, this software can be considered a safe and useful tool as long as it is used responsibly and obtained from a reputable source.
How to install software from the WinRAR file?
To install an application that is in a WinRAR archive, follow these steps:
- Extract the contents of the WinRAR archive to a folder on your computer. To do this, right-click on the archive and select ”Extract Here” or ”Extract to [folder name]”.”
- Once the contents have been extracted, navigate to the folder where the files were extracted.
- Look for an executable file with a .exeextension. This file is typically the installer for the application.
- Double-click on the executable file to start the installation process. Follow the prompts to complete the installation.
- After the installation is complete, you can launch the application from the Start menu or by double-clicking on the desktop shortcut, if one was created during the installation.
If you encounter any issues during the installation process, such as missing files or compatibility issues, refer to the documentation or support resources for the application for assistance.
Can x86 run on x64?
Yes, x86 programs can run on an x64 system. Most modern x64 systems come with a feature called Windows-on-Windows 64-bit (WoW64), which allows 32-bit (x86) applications to run on 64-bit (x64) versions of Windows.
When you run an x86 program on an x64 system, WoW64 translates the program’s instructions into the appropriate format for the x64 system. This allows the x86 program to run without any issues on the x64 system.
However, it’s important to note that running x86 programs on an x64 system may not be as efficient as running native x64 programs. This is because WoW64 needs to do additional work to translate the program’s instructions, which can result in slower performance. Additionally, some x86 programs may not work properly on an x64 system due to compatibility issues.
What is the verdict?
This app is well-designed and easy to use, with a range of useful features. It performs well and is compatible with most devices. However, may be some room for improvement in terms of security and privacy. Overall, it’s a good choice for those looking for a reliable and functional app.
Download Asterisk Password Spy 12 Latest Version Free
Click on the button given below to download Asterisk Password Spy free setup. It is a complete offline setup for Windows and has excellent compatibility with x86 and x64 architectures.