Download HashiCorp Vault Enterprise 1.15 full version program the free setup for Windows. Manage secrets and protect sensitive data. Create and secure access to tokens, passwords, certificates, and encryption keys.
HashiCorp Vault Enterprise Overview
HashiCorp Vault Enterprise stands as a powerful and comprehensive solution for managing secrets and protecting sensitive data in modern IT infrastructures. Developed by HashiCorp, this enterprise-grade tool addresses the critical need for secure and centralized management of secrets, encryption keys, and other confidential information within organizations. The primary focus of HashiCorp Vault Enterprise is to provide a secure, scalable, and dynamic platform that ensures the confidentiality and integrity of sensitive data across diverse environments. The software features a robust and extensible architecture, designed to meet the complex security requirements of modern enterprises. It excels in providing a centralized platform for secret management, allowing organizations to store, access, and control sensitive information, such as API keys, passwords, and encryption keys, in a secure and auditable manner. One of the key strengths of HashiCorp Vault Enterprise lies in its support for multiple authentication methods, including tokens, LDAP, and various cloud provider identities. This flexibility allows organizations to integrate Vault seamlessly into their existing authentication systems, enhancing the overall security posture. The solution also prioritizes the concept of dynamic secrets, generating short-lived credentials on-demand. This approach minimizes the risk associated with long-lived secrets, offering an additional layer of security and reducing the potential impact of credential exposure.
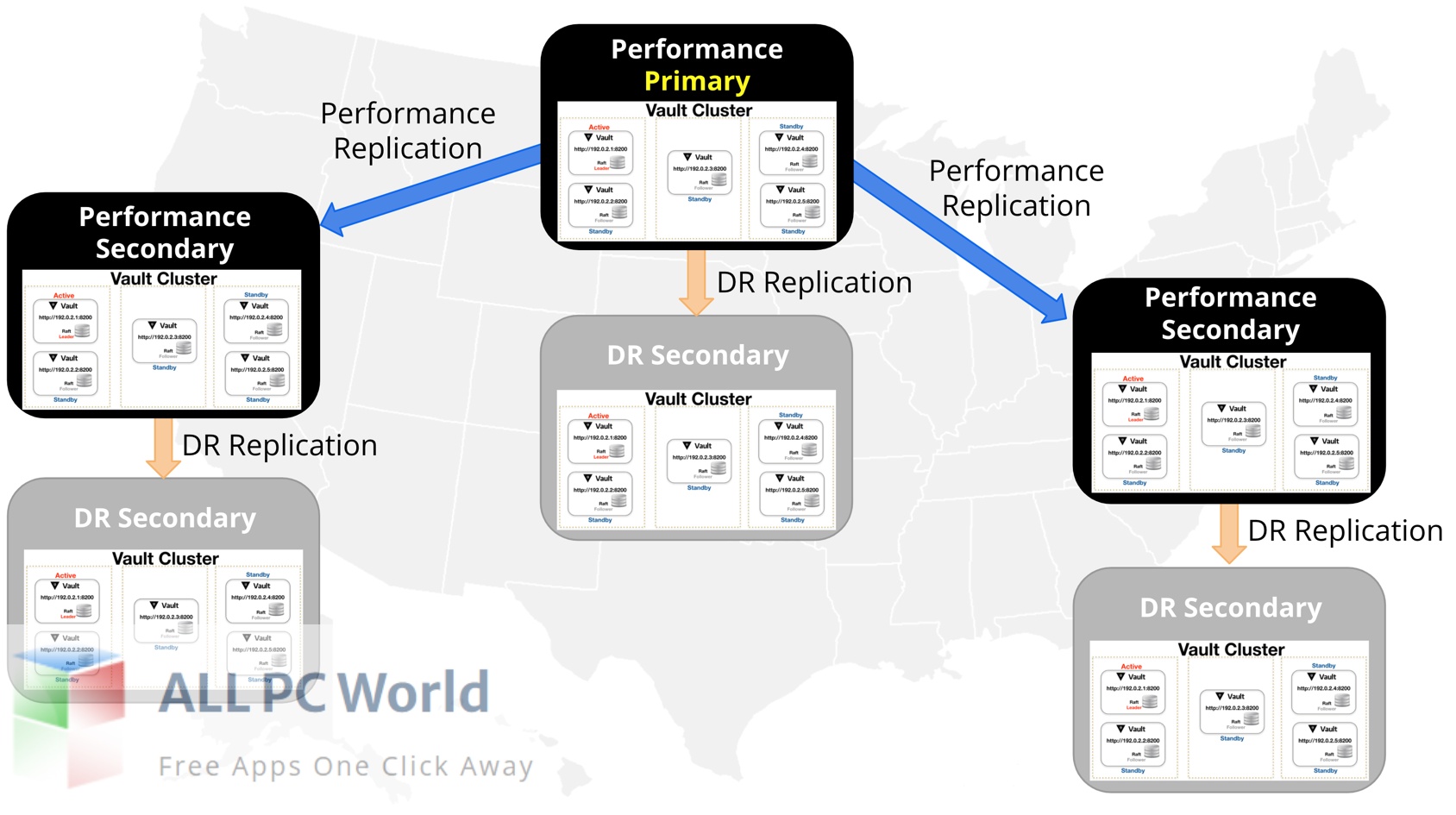
For organizations operating in cloud environments, HashiCorp Vault Enterprise supports dynamic secrets for popular cloud platforms, enabling the secure generation and management of credentials for cloud services. This integration enhances the adaptability of the platform in hybrid and multi-cloud scenarios. Another noteworthy feature is the encryption as a service capability, which allows organizations to centralize the management of encryption keys. This ensures consistent and secure key management practices, contributing to data protection and compliance with industry regulations. Furthermore, the software provides a robust policy framework for access control, enabling organizations to define fine-grained policies that dictate who can access specific secrets and under what conditions. This ensures that access to sensitive information is carefully controlled and auditable. In terms of scalability, HashiCorp Vault Enterprise is designed to handle the needs of large and dynamic infrastructures. It supports high availability and disaster recovery, ensuring continuous access to secrets even in the face of infrastructure failures or disasters. The platform prioritizes security and compliance by offering features such as audit logging, which records all access and modification activities, aiding in compliance audits and security investigations. Additionally, it supports the integration of hardware security modules (HSMs) for enhanced key protection.
In conclusion, HashiCorp Vault Enterprise stands as a robust and sophisticated solution for organizations seeking a secure and scalable approach to secret management. With its extensible architecture, support for various authentication methods, dynamic secrets, encryption as a service, policy framework, scalability features, and emphasis on security and compliance, it provides a comprehensive toolkit for safeguarding sensitive data in dynamic and complex IT environments.
Features
- Centralized Secret Management: Provides a centralized platform for secure management of secrets, including API keys, passwords, and encryption keys.
- Extensible Architecture: Features a robust and extensible architecture designed to meet the complex security requirements of modern enterprises.
- Multiple Authentication Methods: Supports various authentication methods, including tokens, LDAP, and cloud provider identities, ensuring flexibility for integration into existing systems.
- Dynamic Secrets: Generates short-lived credentials on-demand, minimizing the risk associated with long-lived secrets and enhancing security.
- Cloud Integration: Supports dynamic secrets for popular cloud platforms, facilitating secure credential generation and management in hybrid and multi-cloud environments.
- Encryption as a Service: Centralizes the management of encryption keys, ensuring consistent and secure key management practices.
- Policy Framework: Provides a robust policy framework for access control, allowing organizations to define fine-grained policies for accessing specific secrets.
- Scalability: Designed to handle the needs of large and dynamic infrastructures, offering scalability features to accommodate organizational growth.
- High Availability (HA): Supports high availability configurations, ensuring continuous access to secrets even in the face of infrastructure failures.
- Disaster Recovery: Includes disaster recovery capabilities to maintain access to secrets in case of unforeseen events or disasters.
- Dynamic Infrastructure Support: Adapts to dynamic infrastructures, allowing organizations to manage secrets in the context of rapidly changing environments.
- Audit Logging: Records all access and modification activities through audit logging, aiding in compliance audits and security investigations.
- Hardware Security Module (HSM) Integration: Supports integration with hardware security modules for enhanced protection of encryption keys.
- Tokenization: Offers tokenization capabilities for securing sensitive data, replacing actual data with tokens that are then managed by Vault.
- Namespace Support: Provides support for namespaces, enabling organizations to logically segment and isolate secrets based on use cases or teams.
- Secret Versioning: Supports versioning of secrets, allowing organizations to track and manage changes over time.
- Renewable Secrets: Allows for renewable secrets, extending the validity of credentials within defined renewal periods.
- Identity-based Access Management: Enables identity-based access management, tying access permissions to specific identities for enhanced control.
- Secret Cubbyhole: Offers a secure cubbyhole for each authenticated entity, ensuring isolation of secrets for individual entities.
- Secret Revocation: Allows for the revocation of secrets, immediately invalidating compromised or unnecessary credentials.
- Mounting and Backend Support: Supports mounting and backend configurations, providing flexibility in structuring and organizing secrets.
- Namespace Replication: Facilitates namespace replication, allowing for the replication of secrets across different namespaces.
- SSO (Single Sign-On) Integration: Integrates with single sign-on solutions for streamlined and secure user authentication.
- Role-based Access Control (RBAC): Implements role-based access control, defining roles and permissions for different entities within the organization.
- Vault Agent: Introduces the Vault Agent for managing and caching tokens locally, enhancing efficiency and reducing latency.
- Distributed Consensus: Utilizes distributed consensus algorithms for ensuring consistent state across multiple nodes in the Vault cluster.
- API Access: Provides comprehensive API access, enabling integration with other tools and automation workflows.
- Database Secrets Engine: Includes a database secrets engine for secure management of database credentials and access.
- Key Rotation: Facilitates key rotation for cryptographic keys, enhancing security by regularly updating encryption keys.
Technical Details
- Software Name: HashiCorp Vault Enterprise for Windows
- Software File Name: HashiCorp-Vault-Enterprise-1.15.5.rar
- Software Version: 1.15.5
- File Size: 247 MB
- Developers: hashicorp
- File Password: 123
- Language: Multilingual
- Working Mode: Offline (You don’t need an internet connection to use it after installing)
System Requirements for HashiCorp Vault Enterprise
- Operating System: Win 7, 8, 10, 11
- Free Hard Disk Space: MB of minimum free HDD
- Installed Memory: 1 GB of minimum RAM
- Processor: Intel Dual Core processor or later
- Minimum Screen Resolution: 800 x 600
What is the latest version of HashiCorp Vault Enterprise?
The developers consistently update the project. You can view the most recent software update on their official website.
Is it worth it to install and use HashiCorp Vault Enterprise?
Whether an app is worth using or not depends on several factors, such as its functionality, features, ease of use, reliability, and value for money.
To determine if an app is worth using, you should consider the following:
- Functionality and features: Does the app provide the features and functionality you need? Does it offer any additional features that you would find useful?
- Ease of use: Is the app user-friendly and easy to navigate? Can you easily find the features you need without getting lost in the interface?
- Reliability and performance: Does the app work reliably and consistently? Does it crash or freeze frequently? Does it run smoothly and efficiently?
- Reviews and ratings: Check out reviews and ratings from other users to see what their experiences have been like with the app.
Based on these factors, you can decide if an app is worth using or not. If the app meets your needs, is user-friendly, works reliably, and offers good value for money and time, then it may be worth using.
Is HashiCorp Vault Enterprise Safe?
HashiCorp Vault Enterprise is widely used on Windows operating systems. In terms of safety, it is generally considered to be a safe and reliable software program. However, it’s important to download it from a reputable source, such as the official website or a trusted download site, to ensure that you are getting a genuine version of the software. There have been instances where attackers have used fake or modified versions of software to distribute malware, so it’s essential to be vigilant and cautious when downloading and installing the software. Overall, this software can be considered a safe and useful tool as long as it is used responsibly and obtained from a reputable source.
How to install software from the WinRAR file?
To install an application that is in a WinRAR archive, follow these steps:
- Extract the contents of the WinRAR archive to a folder on your computer. To do this, right-click on the archive and select “Extract Here” or “Extract to [folder name]”.
- Once the contents have been extracted, navigate to the folder where the files were extracted.
- Look for an executable file with a “.exe” extension. This file is typically the installer for the application.
- Double-click on the executable file to start the installation process. Follow the prompts to complete the installation.
- After the installation is complete, you can launch the application from the Start menu or by double-clicking on the desktop shortcut, if one was created during the installation.
If you encounter any issues during the installation process, such as missing files or compatibility issues, refer to the documentation or support resources for the application for assistance.
Can x86 run on x64?
Yes, x86 programs can run on an x64 system. Most modern x64 systems come with a feature called “Windows-on-Windows 64-bit” (WoW64), which allows 32-bit (x86) applications to run on 64-bit (x64) versions of Windows.
When you run an x86 program on an x64 system, WoW64 translates the program’s instructions into the appropriate format for the x64 system. This allows the x86 program to run without any issues on the x64 system.
However, it’s important to note that running x86 programs on an x64 system may not be as efficient as running native x64 programs. This is because WoW64 needs to do additional work to translate the program’s instructions, which can result in slower performance. Additionally, some x86 programs may not work properly on an x64 system due to compatibility issues.
What permissions are required for installing the HashiCorp Vault Enterprise?
The permissions required for installing a common Windows program may vary depending on the program and what it does. However, here are some common permissions that a Windows program may require during installation:
- Administrative permissions: Many Windows programs require administrative permissions to install properly. This allows the program to make changes to the system registry, add or remove files and folders, and install drivers or other software components.
- Network access: Some programs may require network access to download additional components or updates during the installation process.
- Access to system resources: Depending on the program, it may require access to certain system resources such as the camera, microphone, or location services. You may need to grant permission for the program to access these resources during the installation process or after the program has been installed.
- Storage access: Programs may require permission to access your computer’s storage to install files or store data.
- User account control: Depending on your UAC settings, Windows may prompt you for permission to install the program. You may need to provide an administrator password or confirm the installation before it can proceed.
What is the verdict?
This app is well-designed and easy to use, with a range of useful features. It performs well and is compatible with most devices. However, there may be some room for improvement in terms of security and privacy. Overall, it’s a good choice for those looking for a reliable and functional app.
Download HashiCorp Vault Enterprise Latest Version Free
Click on the button given below to download HashiCorp Vault Enterprise free setup. It is a complete offline setup of HashiCorp Vault Enterprise for Windows and has excellent compatibility with x86 and x64 architectures.
File Password: 123









